A Software Engineer Wanted to Control His Robot Vacuum with a PS5 Controller but Gained Access to Thousands of Others
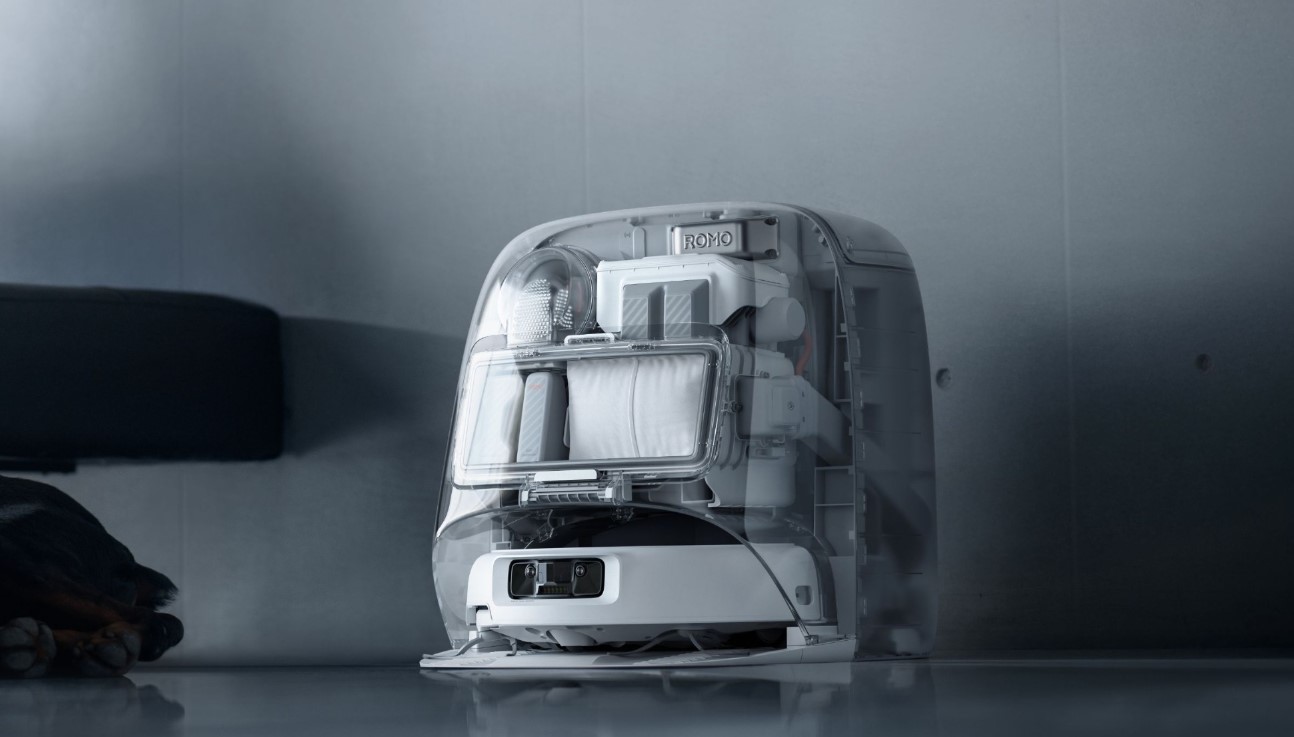
Sammy Azdoufal, a software engineer, recently purchased a DJI Romo robot vacuum priced around two thousand dollars and decided to add some fun by building a custom app to steer it using a PlayStation 5 controller. He turned to an AI coding assistant to reverse-engineer how the device communicated with DJI’s cloud servers. What started as a harmless hobby project quickly revealed a serious security flaw in the system. Instead of limiting access to his own vacuum, the extracted authentication token granted him control over nearly seven thousand other DJI Romo units spread across twenty-four countries.
The vulnerability stemmed from the backend servers failing to properly verify ownership for individual devices. Azdoufal explained that he simply pulled his own private token, the digital key meant to confirm he owned his vacuum, yet the servers treated it as valid for the entire fleet. This meant he could remotely maneuver the robots, check their battery levels, and pull up detailed status information. More concerning, the access extended to live camera feeds from the vacuums’ onboard sensors, allowing real-time viewing inside homes. He could also listen through built-in microphones and generate accurate two-dimensional floor plans showing room layouts.
Azdoufal tested the capabilities carefully, including viewing his own vacuum’s live feed by bypassing its security PIN while waving in front of the camera. He emphasized that he never hacked into DJI’s servers directly, bypassed protections, or used brute force methods. The issue lay entirely in how the company handled authentication on the cloud side. If exploited maliciously, such a flaw could turn these everyday cleaning devices into powerful surveillance tools, exposing private spaces without owners noticing.

DJI, the Chinese manufacturer behind the Romo, confirmed the problem after Azdoufal’s discovery prompted an internal review toward the end of January. The company rolled out patches quickly, with the first system update arriving on February eighth and the final fix completed by February tenth. These updates applied automatically to all affected devices, requiring no action from users. DJI stated they are continuing to enhance security measures to prevent similar issues moving forward.
This incident serves as a stark reminder of the privacy risks tied to smart home gadgets that rely on cloud storage for sensor data like maps and video. Robot vacuums with cameras and microphones offer convenience for navigation and room mapping, but when server-side checks fall short, the consequences can reach far beyond one household. Connected appliances increasingly collect intimate details about daily life, making robust protection essential against unintended or unauthorized access.
What are your thoughts on the security of smart home devices like robot vacuums, and have you ever worried about similar vulnerabilities in your own gadgets? Share your thoughts in the comments.






