Google Unusual Traffic: What Does It Mean And How To Solve It?
Encountering a message about Google Unusual Traffic can be a frustrating experience for any internet user. This notification typically appears when the search engine detects automated requests coming from your network or device. It is a security measure designed to distinguish between legitimate human activity and automated scripts.
Understanding the root cause of this error is essential for maintaining a smooth browsing experience. It serves as a vital safeguard to protect the search engine from potential threats or data scraping attempts. By following the right troubleshooting steps, most users can resolve this issue and return to their normal online activities quickly.
Understanding IP Address Reputation and Search Security
The reputation of your specific network location plays a massive role in how search engines interact with your requests. This concept, known as IP Address Reputation, is a metric used to determine if a particular connection is trustworthy. If multiple people share the same access point, the high volume of queries can trigger a security alert. This is common in public spaces like coffee shops or large corporate offices where many devices connect through a single point.
Sometimes, your internet service provider might assign you a dynamic identifier that was previously used by a malicious actor. When this happens, the search engine remembers the past behavior and flags the current user for scrutiny. Cleaning up this digital history often requires a fresh connection or a temporary wait while the reputation resets naturally. It is a protective measure that treats the connection point as suspicious until the traffic patterns return to a normal state.
Malicious software on a device can also send background requests without your knowledge or consent. These hidden actions contribute to the overall volume of signals that the search engine monitors for safety. Regular system checks help ensure that no unauthorized background processes are affecting your network standing. Keeping your operating system and security software up to date is a primary defense against these invisible traffic spikes.
A sudden change in browsing habits can also influence how your connection is perceived. Performing hundreds of searches in a very short period can mimic the behavior of a bot. If you are conducting intensive research, it is helpful to pace your queries to avoid triggering automated defenses. This demonstrates to the system that the activity is intentional and driven by a human user rather than a script.
Navigating CAPTCHA Challenges and Automated Detection
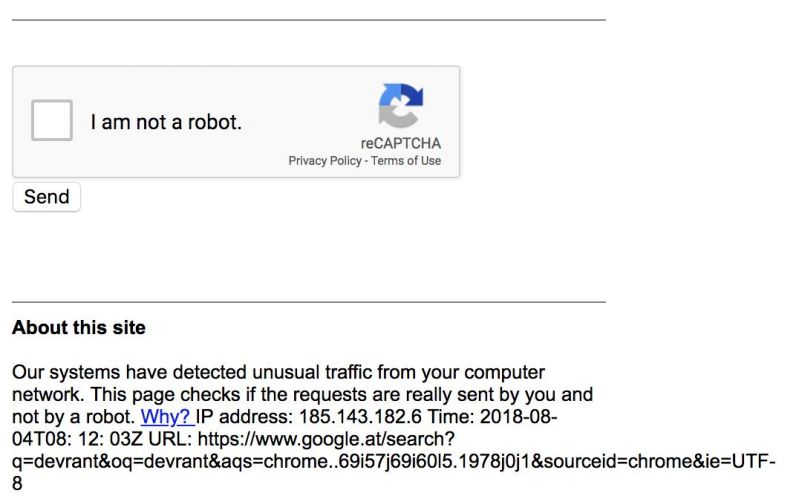
When the system flags a connection, it often presents CAPTCHA Challenges to verify that a human is behind the keyboard. These interactive tests are designed to be simple for people but difficult for automated scripts or bots to solve. Completing these tasks successfully allows you to continue your search activities without further interruption. It acts as a temporary bridge that restores trust between your device and the search engine.
If these verification prompts appear too frequently, it suggests that something in your browsing behavior looks robotic. Rapidly clicking through search results or using specific browser extensions can trigger these security protocols. It is important to adjust your interaction speed to appear more like a standard human visitor. The system is constantly learning from these interactions to refine its detection capabilities and reduce false positives for regular users.
Browser extensions that manipulate search results or harvest data are frequent culprits for these interruptions. Disabling unnecessary plugins can often resolve the issue by streamlining the way your computer communicates with external servers. Keeping your software updated ensures that security protocols remain compatible with the latest search engine requirements. Many users find that a clean browser environment is the most effective way to prevent recurring verification requests.
Persistent verification prompts might indicate a deeper problem with how your device handles cookies or site data. Clearing your browser cache often resets the state of your session and removes stored signals that might be causing confusion. This simple maintenance task is a highly effective first step in troubleshooting connectivity problems. It allows the browser to establish a fresh relationship with the search engine without old data interfering.
The Impact of VPN Usage on Search Queries
Many people utilize privacy tools to hide their location or encrypt their data during online activities. While these services offer excellent security, heavy VPN Usage can frequently trigger warnings from major search platforms. This happens because many users often share the same exit node, leading to a massive spike in requests from a single source. The search engine perceives this concentration of activity as potentially harmful or automated.
If you find yourself blocked while using an encrypted tunnel, switching to a different server location may help resolve the problem. Most providers offer several regional options that might have better reputations or lower traffic volumes at any given time. Testing different connection points allows you to find a server that is not currently being flagged by automated security systems. This simple change is often enough to bypass the unusual traffic warning.
Dedicated addresses provided by privacy services are another way to avoid these common detection issues. By using a unique identifier that is not shared with thousands of other people, you reduce the likelihood of being flagged for suspicious patterns. This approach balances the need for privacy with the requirement for a reliable search experience. It is a premium solution for those who require constant encryption without the annoyance of frequent search blocks.
Some privacy tools also include features that block trackers or modify headers in a way that search engines find suspicious. Reviewing the settings of your privacy software can help you identify if a specific feature is causing the conflict. Disabling certain aggressive filtering options might be necessary to maintain full access to search capabilities. Finding the right balance between anonymity and functionality is key to a smooth internet experience.
Troubleshooting Your Network Configuration and Device Settings
Proper Network Configuration is vital for ensuring that your digital signals are interpreted correctly by external servers. Issues with the way your router handles traffic or DNS settings can sometimes lead to connectivity errors. Verifying that your internal settings follow standard protocols helps prevent these automated search blocks. A well configured network ensures that every request is sent with the appropriate headers and identifying information.
Sometimes, the problem lies with the proxy settings on your local machine or within your browser application. These settings might reroute your traffic through intermediate servers that the search engine finds suspicious. Resetting these options to their default states often clears up any lingering communication errors. It is also wise to check if any third party software has modified your internet settings without your knowledge.
Large home networks with many connected smart devices can also create unexpected traffic patterns. If one device in the household is compromised or malfunctioning, it can impact the search ability of every other device on the same connection. Monitoring your local traffic helps identify any outliers that might be causing the broader network to be flagged. Isolating the problematic device is often the only way to restore normal service to the rest of the household.
Updating your router firmware is a frequently overlooked step in maintaining a healthy internet connection. Manufacturers often release patches that improve security and how the hardware manages outgoing requests. A modern and secure firmware version ensures that your home network remains compatible with web safety standards. Taking the time to perform these updates can prevent a wide range of connectivity issues and improve overall performance.