DJI Will Pay $30,000 to the Man Who Accidentally Hacked Thousands of Their Robot Vacuums
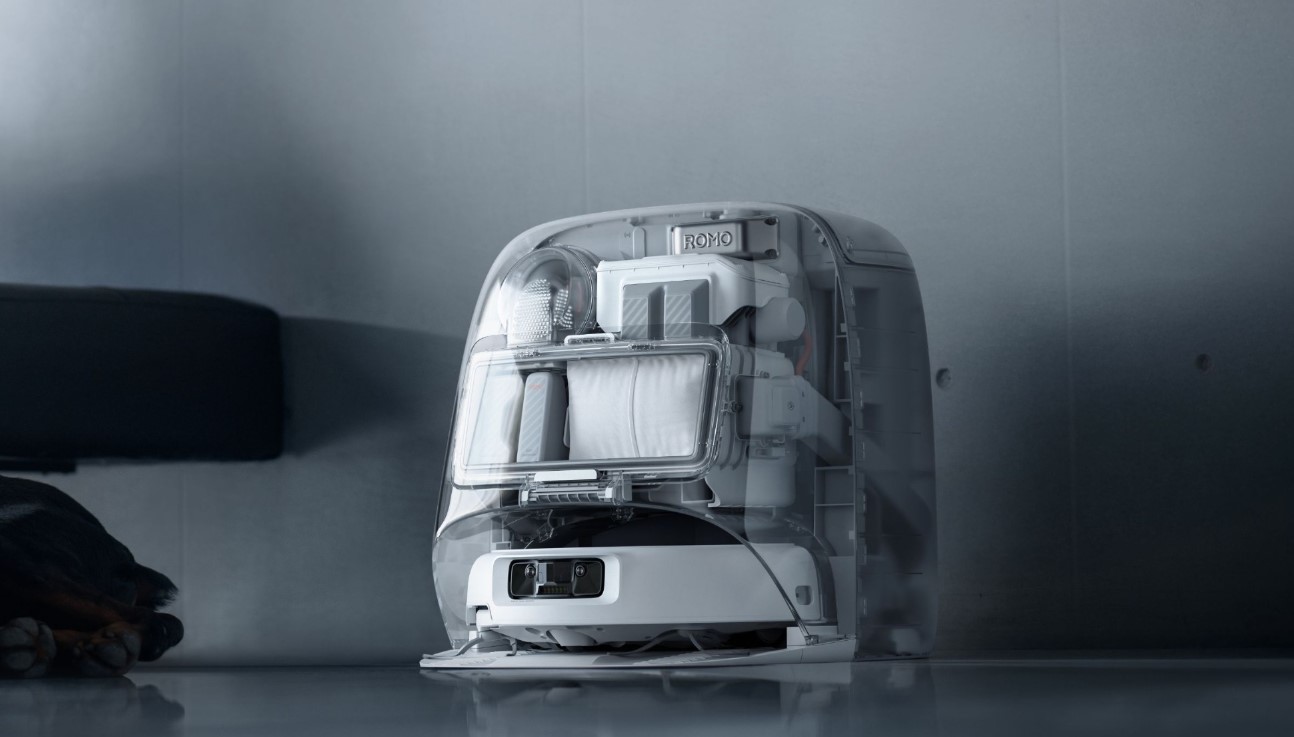
A software engineer named Sammy Azdoufal set out to do something fun with his new DJI Romo robot vacuum. He wanted to control the device remotely using a PlayStation 5 controller. While building a custom app for this purpose, he turned to an AI coding assistant called Claude to help reverse-engineer how the vacuum communicated with DJI’s cloud servers. What started as a personal project quickly turned into the discovery of a major security flaw.
As Azdoufal worked on extracting a security token for his own device, the system granted him far broader access than intended. Instead of limiting credentials to his single vacuum, the backend mistakenly validated his token for thousands of other units. This allowed him to view live camera feeds, listen through microphones, access floor maps, and even see diagnostic data from nearly 7,000 DJI Romo vacuums spread across about 24 countries. The vulnerability stemmed from an authorization issue where the cloud API failed to properly match tokens to specific device IDs, letting anyone with the right manipulation peek into private homes without needing passwords or PINs.
Realizing the seriousness of what he had uncovered, Azdoufal chose not to exploit the access further. He reported the issue responsibly, first sharing details with The Verge, which then reached out to DJI for comment. The company acted swiftly to address the problems. They patched one vulnerability that bypassed the security PIN for viewing video streams and rolled out broader fixes through automatic updates in early February. No user intervention was required, and DJI emphasized that the issues had been resolved.
In recognition of his efforts, DJI has now awarded Azdoufal a $30,000 bug bounty payment for the discovery. The company confirmed rewarding an engineer for the work without initially naming him, though Azdoufal shared the email confirmation publicly. This payout highlights how valuable responsible disclosure can be in improving product security. It also serves as a reminder that connected smart home devices, especially those with cameras and microphones, carry real privacy risks when cloud systems have weak authorization checks.
The incident underscores ongoing concerns in the industry about internet-connected robots potentially becoming surveillance tools if flaws go unnoticed. Azdoufal’s accidental find shows how even well-meaning tinkering can expose widespread vulnerabilities. DJI’s quick response and bounty program demonstrate a commitment to fixing such issues when brought to light.
What do you think about this kind of accidental discovery in smart home tech—would you try modding your own robot vacuum, or does this make you more cautious about connected devices? Share your thoughts in the comments.






